VPN Channel Redundancy: How to Set Up Lightning-Fast Failover Without Downtime
Content of the article
- Why vpn channel redundancy has become critical in 2026
- Active/passive vs. active/active: what’s the real difference?
- Protocols, technologies, and what’s under the hood
- How to detect issues and when to switch
- Failover times: what’s realistic today
- Architectures in practice: from branch to cloud
- Setup checklists: don't forget a thing
- Testing and operations: learning from failures without panic
- Money, licenses, and the economics of fault tolerance
- Common mistakes and how to avoid them
- Real-world cases and numbers
- 30-day step-by-step rollout plan
- 2026 trends: what to watch over 1–3 years
- Mini-guides and handy tips
- Faq: quick and to the point
Why VPN Channel Redundancy Has Become Critical in 2026
The Reality: Clouds, SaaS, and New Points of Failure
We all live in a world where the cloud isn’t just a trend—it’s essential infrastructure. Email, CRM, ERP, billing, code repositories, CI/CD, telephony—they all run over the internet. And when your VPN wobbles, so does your business. A single IKEv2 session freezing for 15 seconds can disrupt chat users, calls, and terminal sessions. In 2026, a "quiet minute" on the network costs way more than it did back in 2019.
Traffic has skyrocketed, reliance on SaaS has increased, and so has the number of remote workers. Before, a rare tunnel reboot was survivable. Now, it’s a blow to your SLA and reputation. That means you need a smart VPN redundancy plan and a well-defined failover scenario—not just some casual setup, but a systematic, measurable one.
Speaking Business: SLA, SLO, and Downtime Costs
Which metric saves the day? SLA and SLO. We set availability goals (say, 99.95%) and translate those into acceptable downtime budgets—minutes per month. Then we calculate the cost of a minute’s downtime for sales, warehouses, and contact centers. The results might surprise you. Even a 300 ms tunnel flap during peak hours can disrupt dozens of payments. So your network shouldn’t just "work"—it must "failover painlessly" at the slightest hiccup from your provider.
Common Topologies and Their Weak Spots
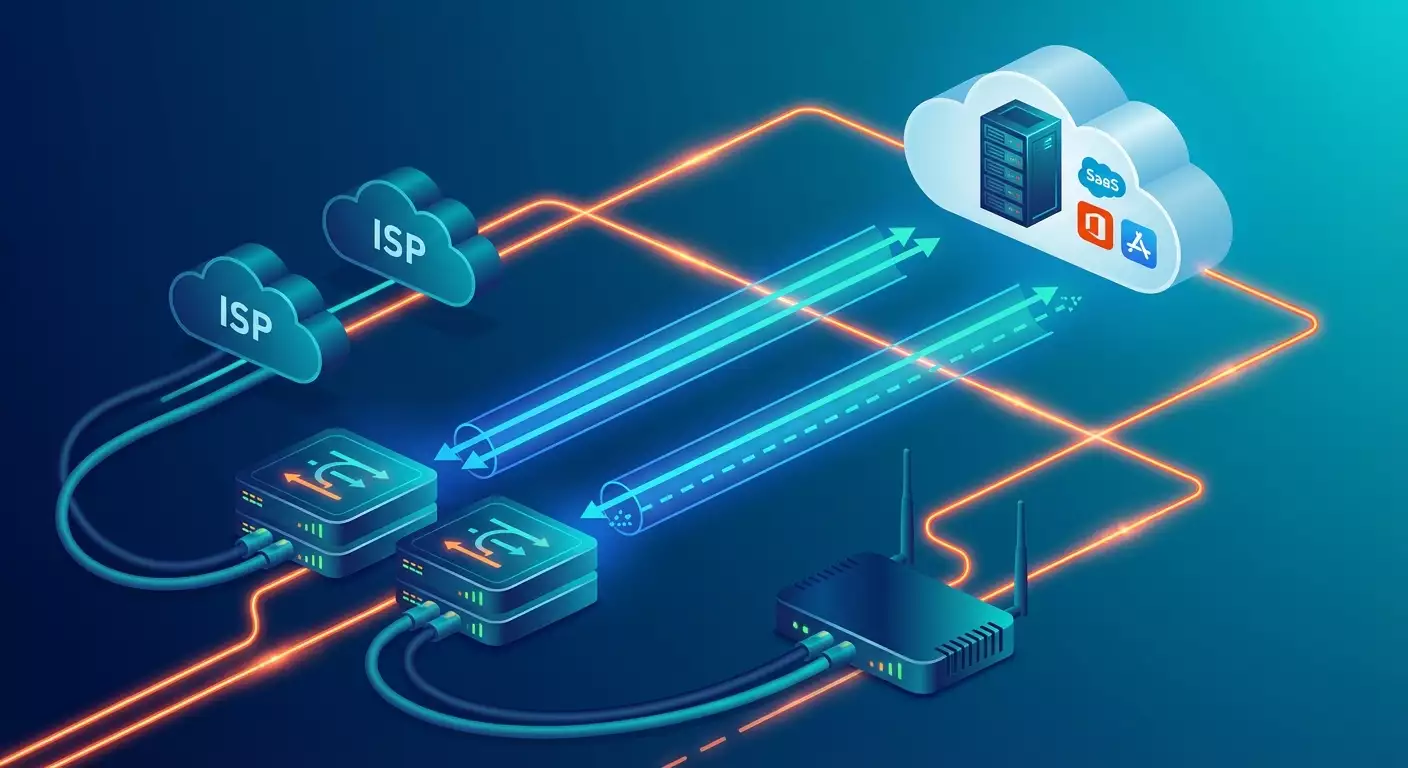
Classic setups: hub-and-spoke with a central data center or cloud, full-mesh between major sites, hybrid with SD-WAN and multiple ISPs, plus LTE/5G as a robust backup link. Vulnerabilities? Routing, NAT, encryption, and security policies often converge in one spot. One bug or a misconfigured timer can trigger a cascade failure. The fix is multilayer redundancy: internet access, routing, tunnels, crypto profiles, even DNS and certificates.
Active/Passive vs. Active/Active: What’s the Real Difference?
Simple Definitions
Active/passive means one channel drives, the other waits quietly. If the primary fails, the backup takes over. Active/active means both channels are active, splitting loads, balancing traffic, speeding things up. Like an airplane with two engines. The key is keeping them synchronized and avoiding route asymmetry.
Pros and Cons of Each Approach
Active/passive is simple, cheap on traffic, and predictable. Downsides: failover always happens and carries some risk of brief session drops. Plus, the backup link can become stale if not regularly tested. Active/active offers higher throughput, faster reaction to issues, and often less latency. Cons include more complex configs, stricter routing and monitoring demands, and the need to manage asymmetry and MTU headaches.
When to Choose What
If any downtime is critical, go with active/active and well-planned path control (ECMP, BGP, Application-Aware policies). If traffic volumes are low but reliability and budget matter, active/passive will serve you well. Sometimes, a mix works best: active/passive for critical apps, parallel active/active for bulk cloud traffic. Hybrids are fine if you keep close tabs on your metrics.
Protocols, Technologies, and What’s Under the Hood
IPsec/IKEv2, WireGuard, SSL VPN: Where They Shine
IPsec with IKEv2 is a mature standard with hardware acceleration, support on enterprise firewalls, VRF, NAT-T, MOBIKE, and strict encryption policies. WireGuard offers minimalism and speed, instant tunnel rebuilds, simple keys, and great performance on ARM and x86. SSL VPN/DTLS is often used for client access and B2B over 443/UDP, flexibly passing through NAT. In 2026, hybrid setups are common: site-to-site on IPsec, employee access via WireGuard or SSL, and SD-WAN overlays using IPsec/DTLS/QUIC.
QUIC and MASQUE: The New Normal for Tunnels
QUIC sits on UDP with built-in encryption and connection management. It's resilient to packet loss, multiplexes streams without head-of-line blocking, and smartly manages congestion. MASQUE lets you tunnel over HTTP/3, masking traffic as regular web data. For failover, this is gold: switching happens faster, sessions suffer less, degradation is softer. Traditional IPsec approaches have caught up somewhat, but QUIC overlays hold an edge in unstable last-mile environments.
Timers and Tunnel 'Heartbeat': DPD, Keepalive, BFD
The magic behind quick failover is proper timer settings. Default DPD in IKEv2 is too gentle: 10–30 seconds. For 2026, that’s an eternity. We set aggressive values: 2–3 seconds intervals, 2–3 retries, capping detection within 4–9 seconds. WireGuard uses keepalive pings every 15–20 seconds for NAT traversal, alongside SD-WAN’s health checks. The fastest detector is BFD—it’s protocol-agnostic and can detect failures in 150–300 ms when properly configured, especially with hardware offload. Paired with BGP, it enables sub-second rerouting.
How to Detect Issues and When to Switch
Channel Health Metrics
It’s not just link up/down. We monitor RTT, jitter, packet loss, MOS for voice, TCP retries, HTTP error rates. In SD-WAN policies, for example: if loss exceeds 2% for 5 seconds or jitter over 30 ms, voice traffic moves to an alternate path. For video calls, thresholds are even stricter. Bulk traffic tolerates up to 5–7% loss but only for 10 seconds max.
Synthetic Probes and Smart Routing
Ping multiple destinations, probe HTTP/HTTPS against real SaaS apps, test DNS, even application-level transactions like CRM logins. Why? The provider might mark the link as up, but traffic to the cloud could be stuck on a congested transit route. The real check is the path to critical services, not generic "internet". App-Aware routing in SD-WAN is powerful: voice goes over the current best path, backup data waits on slower LTE.
Failover Criteria and Anti-Flap
It’s key not to flip-flop constantly. Set hysteresis: for example, switch after 3 seconds of stable degradation, switch back after 15 seconds of stable improvement. Add a slight bias towards the primary to avoid endless traffic bouncing. And yes, log all metrics to monitoring to track decision-making over time.
Failover Times: What’s Realistic Today
Typical Ranges
An IPsec/IKEv2 scenario with aggressive DPD might detect failure in 1–3 seconds plus 0.5–1.5 seconds to reroute—total 1.5–4.5 seconds. Faster? Absolutely. BGP + BFD can detect in 150–300 ms and converge routes in 100–400 ms, summing to 250–700 ms. SD-WAN QUIC overlays with per-flow migration sometimes hit 150–400 ms, nearly invisible to users.
Where Delays Hide
Encryption isn't a bottleneck if you have hardware acceleration. The choke points are control planes: slow timers, heavy ACLs, route asymmetry, double NATs, IPS/IDS restarts, plus DNS and application clients (e.g., SIP may lag slightly during failovers). Inter-module firewall checks often add 0.5–1 second unless you enable fast state synchronization.
Tweaking for Sub-Second Performance
Want failovers that feel almost seamless? Enable BFD for BGP/OSPF, ECMP with per-flow hashing, firewall cluster state sync, QUIC for latency-sensitive traffic, and pre-warmed IPsec SAs (rekey ahead of time, not during outages). Most importantly, test in live conditions—not just during quiet hours.
Architectures in Practice: From Branch to Cloud
Two Providers Plus LTE/5G as Insurance
The branch gold standard: two wired ISPs (e.g., fiber and FTTB) plus a third leg—LTE/5G. Wired links run active/active to split traffic; mobile sits as a passive backup. Prioritize carefully: voice and ERP never fall to mobile unless it’s a disaster. Bulk file transfers avoid mobile altogether. Your bills will thank you.
Hub-and-Spoke with a Cloud Center
If your hub’s in the cloud, build dual ingress: IPsec to two regions of the same provider or different clouds (multi-cloud) with Anycast entry addresses. Use BGP over IPsec, enable BFD, and deploy firewall clusters with VRRP/HA on endpoints. Sounds complex, but you'll get regional failover in seconds, not minutes.
Full SD-WAN for a Global Company
SD-WAN offers application-aware policies, flexible telemetry, and overlays over any underlay: MPLS, DIA, LTE/5G, even LEO satellite. In 2026, many vendors natively support QUIC and MASQUE, NBAR2 app parsing, SLA management across hundreds of prefixes. The key: never lose control. Document traffic classes, failover conditions, and regularly run degradation tests.
Setup Checklists: Don't Forget a Thing
Planning and Addressing
Segment networks and VRFs upfront to avoid fixes in production. Plan IP subnets, list critical applications, and prioritize SLA classes (voice, video, transactions, backups). Define MTU and MSS, verify Path MTU Discovery, and budget 60–80 bytes for encryption overhead (exact size depends on protocol and options).
Routing and Policies
Choose static or dynamic routing (BGP/OSPF). For dual paths, use BGP + BFD. Enable ECMP for active/active. For active/passive, configure preferences and weights. Add policy-based routing when IP addresses aren’t enough but app classes are clear.
Timers, Health Checks, and Failback
Set DPD to 2–3 seconds, 2–3 retries. BFD example: 200 ms interval, 3 failures. Anti-flap at 10–20 seconds before switching back. Separate SLA thresholds for voice/video vs. bulk. Prefer synthetic HTTP probes to real services over just ICMP to 8.8.8.8.
Monitoring and Logging
Enable NetFlow/IPFIX with export to NTA/NPM, collect metrics in Prometheus, traces in OpenTelemetry, and alerts via chatbots. Log failover events, reasons, durations, and affected traffic classes. Optimizing blindly is painful—don’t do it.
Testing and Operations: Learning from Failures Without Panic
Playbooks and SLOs
Define SLOs for time to detect (TTD) and time to recover (TTR). Document playbooks: who does what on degradation, which commands to check, what to restart, who to notify. A simple checklist saves you hours and money.
Chaos Testing During Business Hours
It’s scary but effective. Plan controlled degradation: induce 3% loss on primary channel and watch voice shift to backup. Disable one underlay and verify session persistence. Don’t do this Friday evening—but do it regularly.
Postmortems Without Blame
After incidents, review what really happened: which timers triggered, what slowed response, where faster action was possible. Fix the small stuff and document lessons. Networks are living systems. First-time perfect setups don’t exist—and that’s okay.
Money, Licenses, and the Economics of Fault Tolerance
CAPEX and OPEX Made Simple
Two providers, plus LTE/5G, plus SD-WAN or VPN gateway licenses sound costly. But calculate TCO vs. downtime costs. Often, one major incident pays for a year of licenses. And if you’re sending couriers with paper just because VPN dropped? Welcome to accounting nightmares.
Where to Save and Where Not To
Don’t skimp on monitoring and backup SIM cards. Save on features you won’t use (e.g., Layer 4 DPI if you already have NTA). Compare mobile plans carefully and factor in burst traffic during outages.
Licenses and Hidden Limits
Many vendors cap tunnels, BFD sessions, and App-Aware policies. Check the limits tables before buying or your beautiful design won’t fly. Also, verify if QUIC/HTTP3 and MASQUE are included in your software edition—in 2026, they’re common but not always default.
Common Mistakes and How to Avoid Them
MTU, MSS, and Fragmentation
This is the top cause of weird bugs. Tunnels add overhead, MTU drops, packets break, apps cry. Set MSS clamp to 1360–1380 for TCP over IPsec/SSL, test PMTUD, and monitor the DF bit. Better to spend an evening testing than a week chasing phantom bugs.
Route Asymmetry and Firewall State
Active/active is great, but asymmetry kills. If inbound happens on one link, outbound on another, stateful firewalls might drop packets. Enable state sync in firewall clusters, use per-flow ECMP, monitor hashing (5-tuple), and avoid unexpected PBR exceptions.
Default Timers
Defaults aren’t your friends. DPD at 10–30 seconds, BGP without BFD, DNS TTL at an hour—all make failover slow and painful. Configure aggressively but with anti-flap. Test scenarios ahead. We don’t buy a sports car just to leave the speed limiter at 40 km/h.
Real-World Cases and Numbers
Retail: 200 Stores, LTE as Lifeline
A retail chain moved to dual DIA + LTE/5G backup. For POS and acquiring, strict SLAs were set (loss <1%, RTT <120 ms). LTE failover happens in 1–2 seconds, keeping payments flowing; max auth delay is 0.3–0.5 seconds. Traffic costs rose 8% YoY, but checkout downtime incidents dropped 92%.
SaaS Developer: Global SD-WAN and QUIC
The R&D team spans six countries. They rolled out SD-WAN with QUIC overlays for Git, CI/CD, and video calls. Switching between backbones takes 150–300 ms. A transit provider outage in Europe was only visible on charts—users didn’t notice. They cut complaints by 40% with proper policies and thresholds.
Call Center: BGP + BFD for Voice
A contact center with 400 operators uses IP telephony and thin clients. Before BFD, failover took 6–8 seconds, killing calls. After, it dropped to 200–400 ms. Most work was cleaning QoS tags and tuning anti-flap, not "magical" hardware.
30-Day Step-by-Step Rollout Plan
Week 1: Inventory and Goals
Gather lists of providers, tunnels, addressing plans, apps, and metrics. Define SLOs: voice TTR under 1 second, web under 3, backups allow 30 seconds. Assign responsibilities.
Week 2: Pilot and Timers
Build a pilot at two sites: enable BFD, shorten DPD, set up ECMP or active backup. Activate NetFlow, synthetic HTTP probes, chat alerts. Simulate loss/jitter degradation, review charts and failover logs.
Week 3: Security and Clusters
State sync in clusters, proper NAT, refine IPS/IDS, minimize checks on failover traffic. Update crypto profiles (AES-GCM, PFS, key attestation), explore hybrid post-quantum profiles if your vendor supports IKEv2 PQC hybrid.
Week 4: Scale and Regulations
Roll out to all branches, document playbooks, schedule regular degradation tests, configure CFO and CIO reports: failover counts, time savings, saved calls and transactions. This isn’t just a network—it’s a business tool.
2026 Trends: What to Watch Over 1–3 Years
Widespread QUIC and MASQUE Adoption
More vendors tunnel over HTTP/3. Hiding under 443/UDP boosts pass-through and offers real flexibility during degradation. We’re seeing mixed scenarios: IPsec for B2B, QUIC overlays for voice and video.
Deeper App-Awareness
SD-WAN now recognizes application states: signaling, media streams, data. Policies are smarter, switches smoother, fewer unnecessary migrations. This saves money on backups and boosts stability.
Post-Quantum Algorithms in IKEv2
Hybrid handshakes are appearing in enterprise products. It’s still early, but will soon become a compliance must-have in some industries. Budget plenty of crypto processing power.
Mini-Guides and Handy Tips
Provider Selection and Diversification
Choose diverse routes, different entry points, ideally distinct backbone operators. Check whether your two ISPs actually share a third-party tunnel. Demand SLAs with real penalties, not vague promises.
QoS and Marking
From ingress port to tunnel and back. Preserving DSCP is critical; without it, voice competes with backups after failover. Verify label rewriting in tunnels and NAT boundaries. Enable policies against "evil" large queues.
Documentation, But Without the Horror
One page per service: SLA goals, critical dependencies, backup paths, timers, provider contacts. Update quarterly. Nobody loves documentation, but when everything’s on fire, it’s your best friend.
FAQ: Quick and To the Point
What’s a “good” VPN failover time in 2026?
For voice and video—aim for 150–700 ms (BFD, ECMP, QUIC). For general web apps, 1–3 seconds is acceptable. Anything over 5 seconds is noticeable and triggers user complaints.
Is active/active always better than active/passive?
No. It’s more complex, costlier to operate, and demands routing and firewall state management. If traffic is small and budget tight, a “good” active/passive with aggressive timers can deliver excellent results.
Can fast failover be achieved with “bare” IPsec without SD-WAN?
Yes. BGP + BFD over IPsec, proper DPD, aggressive rekey, state sync, and ECMP can get you into sub-second failover territory in most cases. SD-WAN adds convenience and app awareness but isn’t mandatory.
Should backup channels always carry traffic?
Partially, yes. Health traffic and light loads keep channels from becoming idle. A completely empty backup often surprises you when the time to shine comes.
How do you know failover is truly seamless for users?
Measure not just RTT/loss but user experience metrics: page load times, transaction success, MOS, media jitter. Add surveys, NPS scores, and ticket analysis. Only a complete data set tells the real story.
Is it worth moving critical apps to QUIC?
If your vendor supports it and you’re ready to test, yes—it offers packet loss resilience and fast recovery. But QUIC doesn’t replace good routing and redundancy. It’s a booster, not a magic wand.
What if providers use the same route?
Look for alternatives: microwave links, LEO satellite, LTE/5G. Sometimes “different” providers on the same backbone is just illusion. Insist on proof of physical route diversity.
