Mesh VPN vs Hub-and-Spoke: How to Choose Between Tailscale, ZeroTier, and the Classics
A comparison of Mesh VPN and Hub-and-Spoke architectures: Tailscale and ZeroTier versus IPsec, DMVPN, and SD-WAN. Pros and cons, performance, security, use cases, practical tips, and 2026 trends for networks, DevOps, and business.
Content of the article
- Why even debate: mesh vs hub-and-spoke
- Architecture deep dive: under the hood
- Tailscale and zerotier vs classics: what’s really different
- Mesh vpn pros and cons: an honest look
- Hub-and-spoke pros and cons: control and predictability
- Performance: latency, bandwidth, cpu, and mtu
- Security and zero trust: identity, policy, and inspection
- Use cases: when mesh, hub, or hybrid?
- How to choose: checklist and simple rule
- Hybrid topologies: best of both worlds
- Use cases and numbers: real-world insights
- Practical steps and pitfalls
- Trends 2025-2026: where it’s heading
- Conclusions: a simple decision matrix
- Faq
Why Even Debate: Mesh vs Hub-and-Spoke
When building a virtual network, the main decision seems straightforward: mesh VPN or hub-and-spoke. But beneath that simplicity lie many nuances. How can we reduce latency without losing control? How do we seamlessly blend clouds, branches, remote workers, and an IoT fleet without headaches? And—most importantly—how do we make sure the network doesn’t fall apart when it matters most?
We’ll break down both architectures, compare Tailscale and ZeroTier against traditional IPsec, DMVPN, and SD-WAN methods, dive into performance, security, management, cost, and provide a practical checklist. No fluff—just useful details, real-world experience, and honest trade-offs. This isn’t about religious debates; it’s an engineering decision with costs, risks, and benefits.
Quick summary: mesh offers flexibility and minimal latency between nodes, while hub-and-spoke provides control, predictability, and compliance. The choice depends on traffic, people, budget, and the rules of the game. Just like in life.
Brief Definitions
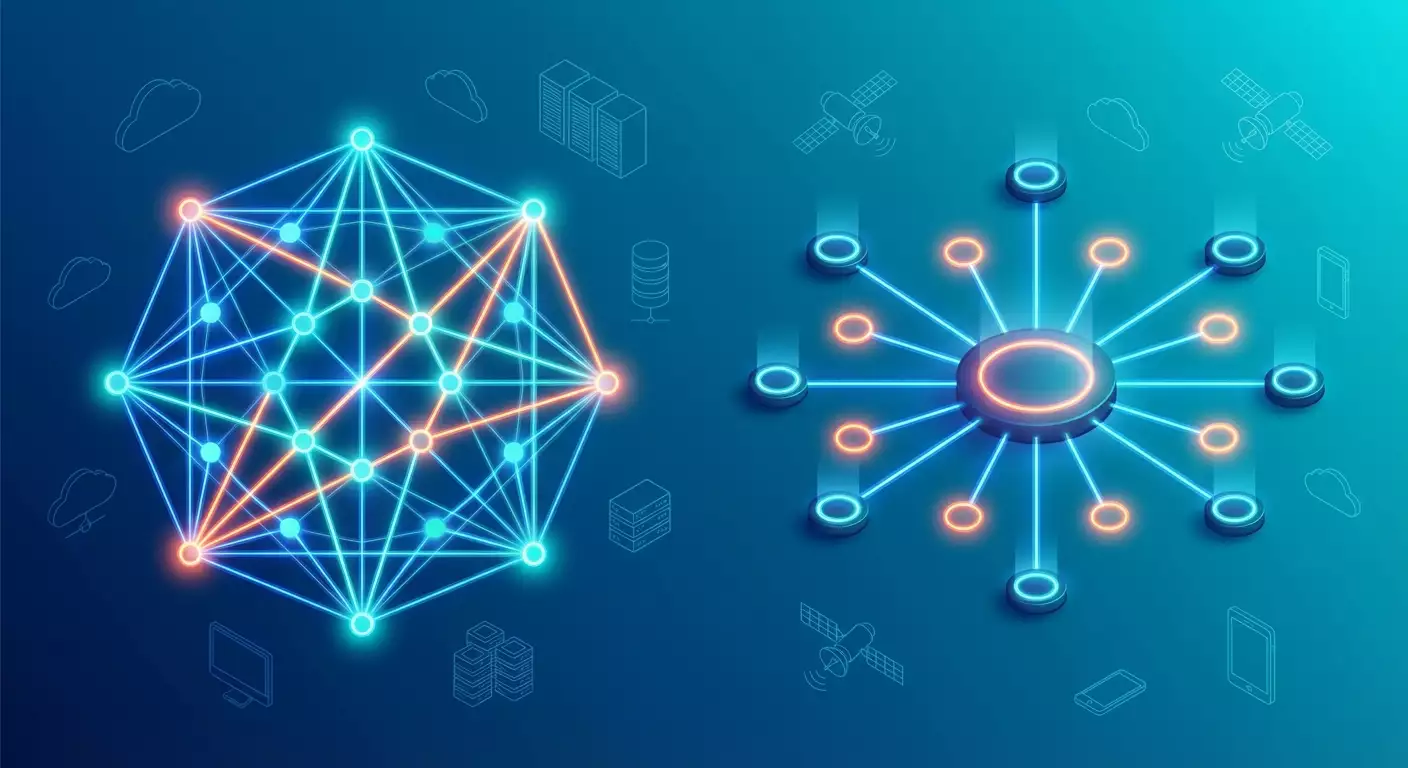
Mesh VPN—each node can establish a direct encrypted connection to another node. Minimal packet zig-zags. Technologies include WireGuard overlays, P2P, DHT, STUN, and TURN-like relays.
Hub-and-Spoke—all connections route through central hubs. Nodes don’t communicate directly but connect to a focal point. Technologies include IPsec site-to-site, DMVPN with NHRP, SD-WAN with controllers, centralized routing, and policies.
The Core Dilemma
You either prioritize edge performance and autonomy or choose a unified gatekeeper with strict control and easy audit. Trade-offs are inevitable. That’s why hybrids are trendy now. We’ll get to that shortly.
Architecture Deep Dive: Under the Hood
Mesh: Peer-to-Peer, Routing, and NAT Traversal
In mesh networks, nodes discover others via a coordinating control plane and try to set up direct tunnels. Success depends on NAT types, firewalls, and policies. Gamers called this NAT bypass; in VPNs, it’s NAT traversal. UDP is almost always used, with frequently refreshed short keys; routing is configured as an overlay atop the existing network.
The mechanics often rely on WireGuard channels—a lightweight, fast, minimalist protocol well-suited to modern CPUs. The catch? It’s not always possible to punch through a strict corporate perimeter. Then a relay server (like TURN/DERP) is needed—adding latency but ensuring connectivity. If peer stitching succeeds, latency drops, and packets travel the shortest path.
Hub-and-Spoke: Predictable Routes and a Unified Perimeter
Central hubs are routers or VPN gateways, often with hardware encryption acceleration and advanced traffic inspection. Branch networks reach resources through the hub. The control plane might be on-premises, cloud-based, or hybrid. Security policies, NAT, routable networks, segmentation—all converge at one point, ideal for logging and auditor reports.
Routing-wise, it simplifies life: BGP or static rules clearly define traffic flow, and hairpinning through hubs keeps things orderly. Yes, packets take detours, but you know exactly where and how they’re controlled. For many industries, this is critical.
Zero Trust Across Both Paradigms
Whether star or mesh, modern networks in 2026 lean toward ZTNA. User and device identity comes first; the network is second. We don’t allow traffic based on IP but on “who” and “why.” This is natural in mesh: node-as-identity, policies at the identity layer. In hub-and-spoke, it’s implemented via proxy access, segmentation, NPU-accelerated inspection, directories, and SSO.
Tailscale and ZeroTier vs Classics: What’s Really Different
Tailscale: WireGuard, Identity, and Simplicity
Tailscale uses WireGuard as its data plane and focuses on identity: you log in a device via SSO, it gets keys, and you’re set. The network looks like a private overlay (tailnet), and ACLs are written in a human-friendly language. The magic is automatic NAT traversal and fallback relays, plus built-in DNS, MagicDNS, and exit nodes. The entry barrier is low, the admin interface friendly, and policies declarative. Limitations? Local traffic inspection is trickier, complex L2/L3 scenarios require workarounds, and highly centralized egress/control points need planning.
ZeroTier: Virtual Switches and an SDN Style
ZeroTier feels like mini-SDN: virtual networks, flow-level rules, capable of both L3 and L2 overlays where needed. It plays well with IoT and distributed nodes, easily layering a network over any internet—from 4G to satellite. ZeroTier’s flexible topology control is a plus. Downsides are similar: centralized perimeter and inspection aren’t default, you need designated egress nodes, and strict regulatory compliance demands extra components.
The Classics: IPsec, DMVPN, SD-WAN
IPsec site-to-site is a trusty workhorse, time-tested, auditor-friendly, and hardware-supported. DMVPN adds dynamism: spoke-to-spoke via NHRP, edging toward mesh experience but with hub control. SD-WAN brings app management, QoS policies, and invisible channel selection magic. Powerful but sometimes burdensome: costly hardware, licenses, custom agents, and configs hundreds of lines long.
Mesh VPN Pros and Cons: An Honest Look
Performance and Latency
Mesh usually wins latency when peers connect directly—no hub hairpins, the route is short, and TCP congestion adapts faster. Real-life cases showed a 20-40% RTT reduction between developers across countries. But not always: if a relay is needed, latency jumps. Also, with many nodes, "all-to-all" potential sessions can explode.
Scaling and Control
At small to medium scale, mesh is pure joy. For hundreds or thousands of nodes, control panels become crucial: who talks to whom and why? Here, platforms with strong ACLs, tags, roles, audit, key rotation, and clear discovery shine. Without discipline, mesh may turn into "spaghetti networks" in large orgs.
Reliability and Failover
A mesh’s strength is no single point of failure in the data plane. Rain starts? Nodes regroup. One relay fails? Another picks up. The control plane, like with any managed solution, must remain available. Plan offline behavior, ACL caching, signaling backups, and consider how critical supplier cloud outages are.
Security and Compliance
Identity by default, minimal open ports, small attack surface—that’s good. Yet industry standards often require inspection: IDS/IPS, DLP, SSL/TLS decryption, session recording. Pure P2P struggles here. So exit nodes with inspection or proxy nodes are used—a hybrid that works well.
Hub-and-Spoke Pros and Cons: Control and Predictability
A Unified Perimeter and Simple Logic
One or several hubs as "gateways" is every auditor’s dream: centralized logs, centralized inspection, neat segments, predictable routes. Need a DMZ? No problem. Force traffic through an NGFW? One rule does it. It’s convenient, especially where businesses operate under regulation.
The Cost of Control: Latency and Hairpinning
The downside is clear: every inter-branch flow takes a detour. If your offices are in Sydney and Tokyo with a hub in Europe, users notice—especially real-time apps. Mitigated by regional hubs, smart SD-WAN, and caching, but it adds cost and complexity.
Reliability and Scale
Hubs are critical nodes duplicated with active-active or active-passive, clustered, hardware accelerated for encryption, fast disk logging, dedicated uplinks. Well implemented, they’re rock-solid. Ownership cost rises though: licenses, support, hardware upgrades, and internal expertise. But you always know where and how things run.
Flexibility for Applications
Hub-and-spoke handles ad-hoc communications poorly. Need to connect a tester’s laptop to a temporary cloud environment directly? Bureaucracy ensues: requests, policy changes, maintenance windows. Mesh does this in minutes; hub-and-spoke, in hours. If you have agile teams, it’s painful. If you’re a conservative bank, it’s a feature.
Performance: Latency, Bandwidth, CPU, and MTU
Latency: Shortest Path vs Central Node
Mesh wins with the shortest path. In 2026, average cloud region RTTs hover around tens of milliseconds; every extra transit adds a percentage. With strict NAT requiring relay, mesh loses advantage. Hub-and-spoke latency is stable and predictable, letting you plan QoS.
Bandwidth and Encryption
WireGuard on modern CPUs easily delivers hundreds of Mbps per stream. IPsec with AES-NI hardware can reach gigabits, especially on dedicated hardware. SD-WAN uses NPU acceleration. Which is faster? Depends on node and role. For a developer’s laptop pulling git from abroad, mesh on WireGuard often wins. For a 10 Gbps office channel with centralized filtering on hardware IPsec, hub-and-spoke dominates.
MTU, Fragmentation, and UDP
Overlays tend to eat into MTU. Without PMTU discovery and MSS clamping configured, you’ll see odd freezes. UDP traffic on the internet fares better than five years ago thanks to networks adapting to QUIC and gaming. Local filters still exist. Rule of thumb: test with real apps, not just iperf.
Stability with Packet Loss
Mesh’s direct routes rely less on congested backbones but are more sensitive to specific ISP quality pairs. Hub-and-spoke supports advanced SD-WAN features like FEC, packet duplication, and jitter buffers. These cost extra but really help voice/video resilience.
Security and Zero Trust: Identity, Policy, and Inspection
Identity Beyond Networks
By 2026, auth mostly goes through SSO, FIDO2, and conditional policies. Mesh solutions integrate this naturally: access isn’t IP based but “who you are” and “device state.” Hub-and-spoke uses proxies, NAC, micro-segmentation, and strict inter-segment rules.
Inspection, Compliance, and Traffic Recording
Needing full inspection? Hub-and-spoke is easier: all traffic passes through NGFW, IDS/IPS, DLP. Mesh does spot inspection: exit nodes for internet egress, local proxies for critical apps, app-level logs. This demands architectural planning, or you risk overlooked "side paths."
Keys, Rotation, and Quantum Resistance
WireGuard and modern IPsec profiles offer strong cryptography. Key rotation, certificate management, secret storage, and stolen device tracking are essential. In 2026, many companies pilot hybrids with post-quantum algorithms at the control plane and classical ciphers at data plane. No rush, but preparation is key.
Microsegmentation and Least Privilege
Broad network segmentation is outdated. Micro-level wins: access is service-to-service or user-to-service, not subnet-to-subnet. Mesh uses identity-based ACLs; hub-and-spoke leverages NGFW policies, security groups, and tags. The outcome: minimum access, maximum visibility.
Use Cases: When Mesh, Hub, or Hybrid?
Remote Work and Development
Mesh shines here. Developers, QA, and SREs connect laptops, build agents, self-hosted runners, and test environments with no hassle. Access is up in minutes; ACLs are GitOps style; routes just work. Need inspection? Add exit nodes for checks.
Branches, ERP, and Traditional Offices
Office printers, IP telephony, terminal services—a hub-and-spoke classic. Centralized control, channel redundancy, voice/video prioritization. SD-WAN ensures quality, IPsec handles encryption, NGFW enforces policies. Network teams happy, auditors smiling.
Multi-Cloud, B2B, and Partner Networks
Cloud-to-cloud hybrids love mesh: connecting VPCs, Kubernetes clusters, databases, caches across regions without long transits. External partner integration leans on policy and audit, benefiting from a dedicated hub filtering external access while mesh serves internal teams.
IoT and Manufacturing
Depends on scale. For tens or hundreds of devices, mesh via ZeroTier or similar works well over 4G/5G. For thousands with strict OT security, centralized gateways, segmentation, and specialized brokers are better. Physical access control and secure boot matter more than mesh vs hub debate.
How to Choose: Checklist and Simple Rule
Identify Traffic Patterns
Who talks to whom? User to app? App to app? Database to backup? If ad-hoc node interactions dominate—mesh. If 80% of traffic exits through one perimeter—hub.
Security and Audit Requirements
Need full inspection and logging? Want straightforward regulator reports? Choose hub-and-spoke with NGFW, proxy, and familiar telemetry. If audit is flexible and risks are managed via identity and apps—mesh with targeted inspection fits well.
Team and Budget
Got network engineers who love BGP, IPsec, and fine tuning? Hubs will please them. DevOps and SRE teams seeking declarative, fast access management will favor mesh. Costs vary: cloud mesh often cheaper to start; classics pricier on hardware but sometimes better at scale.
The Simple 70/30 Rule
When in doubt, go hybrid: 70% of traffic via hubs for control, 30% mesh for developer agility and automation. Rebalance as your processes mature.
Hybrid Topologies: Best of Both Worlds
Mesh for East-West, Hubs for North-South
Internal services talk mesh to avoid hub detours. All internet egress and external integration flows through hubs with IDS/IPS and DLP. Routing and DNS split responsibility domains. This is common among product companies.
Relay Nodes, Exit Nodes, and Proxies
When direct peer connections fail, mesh falls back on relays. Plan relay geography carefully. Add exit nodes with proxies and malware protection for groups needing secure internet access. Choose regions wisely to avoid needless ocean hops.
SD-WAN Underlay and Overlay Mesh
A winning combo: SD-WAN provides a reliable SLA-backed underlay between offices and cloud nodes; mesh overlays offer fast peer-to-peer connections where flexibility matters. The result: high-level "controlled chaos" in a good way.
Route Awareness and BGP
Sometimes it makes sense to announce mesh routes into controlled domains via BGP on hubs. This way, the "outside world" sees your private networks, while mesh handles specific peers. Just don’t mix announcements and avoid routing asymmetry.
Use Cases and Numbers: Real-World Insights
Distributed Product Company
Teams in Europe, Asia, and Latin America. Developers running containers, CI/CD, tests. Switched to mesh over WireGuard. Result: 25% faster releases as build agents fetch artifacts quicker from nearby nodes. Security? Identity-based ACLs, MFA, conditional policies. Internet egress via a couple of inspected exit nodes. Cost? Reduced central gateway bills and simplified onboarding.
University Network and Labs
Labs scattered across campuses. Previously hub-and-spoke with long exception lists. Moved to hybrid: local mesh segments between labs and central hub for internet and external integrations. Scientists happy—latency down, configs smoother. InfoSec retained control over critical flows.
Retail Branch Network
Thousands of stores, cash registers, scanners, guest Wi-Fi. Stayed with hub-and-spoke plus SD-WAN and NGFW. Simple reason: single internet channel, mission-critical cash systems, strict audit. Mesh couldn’t provide needed centralized inspection without complexity. Result: reliability prioritized, latency secondary.
IoT in Manufacturing
Sensors, cameras, controllers. Lightweight mesh used for maintenance and diagnostics, while operational traffic flows through industrial gateways. Strict segmentation and logging. Achieves fast device access without jeopardizing the industrial network.
Practical Steps and Pitfalls
Quick Start with Mesh
Step 1: Enable SSO, MFA, and basic posture policies. Step 2: Define device tags and groups. Step 3: Write ACLs by services, not subnets. Step 4: Assign one or two exit nodes with inspection for internet-bound groups. Step 5: Check MTU and MSS clamping. Step 6: Test with real apps, not just ping.
Quick Start with Hub-and-Spoke
Step 1: Select hubs by region and ensure redundancy. Step 2: Define security zones and inter-zone policies. Step 3: Deploy IPsec/DMVPN or SD-WAN profiles supporting your traffic. Step 4: Enable logging, SIEM export, alerts. Step 5: Test failover and quality degradation. Step 6: Document everything to avoid reliance on a few "guru engineers."
Common Pitfalls
MTU and fragmentation are classic issues. DNS inconsistencies cause weird bugs. Asymmetric routing hurts. And never underestimate the human factor. Provide teams clear roles and fast access procedures. Don’t skimp on observability: telemetry is your best friend.
Observability and SLOs
By 2026, measuring network SLOs is standard: target RTTs, loss, control plane availability. In mesh, add NAT traversal success and relay traffic percentage metrics. Hub-and-spoke tracks hub load, queues, encryption performance, IDS misses. Observability must serve business goals, not the other way around.
Trends 2025-2026: Where It’s Heading
Convergence of SASE, SD-WAN, and Mesh
Vendors blend the best of all worlds: flexible edge mesh, cloud inspection points, identity-driven policies. Teams get simplicity, security, and predictability without sacrificing delivery speed.
eBPF and Edge Acceleration
eBPF kernel paths, user-space stacks, zero-copy—no longer exotic. Mesh networks benefit on mass client devices, hubs get hardware boosts. Result: less overhead, more throughput.
Ubiquitous QUIC and UDP Friendliness
Networks have adapted to QUIC. Middleboxes smarter. For mesh, this is a gift: UDP passes easier, fallbacks happen less. Still, relays stay handy—Murphy’s law lives on.
Identity and Post-Quantum Readiness
Companies roll out key rotations, hardware vaults, device attestations. On the horizon: hybrid key exchanges and post-quantum pilots. No panic yet, but preparation is time-critical.
Conclusions: A Simple Decision Matrix
When to Choose Mesh
You need speed, flexibility, development agility, temporary environments, multi-cloud east-west traffic, IoT management, and minimal bureaucracy. Key metrics: feature velocity and team autonomy.
When to Choose Hub-and-Spoke
Strict control, traffic inspection, compliance, large branch networks, and predictability are priorities. Key metrics: stability, audit readiness, SLA for critical apps.
When to Choose Hybrid
Almost always. Split traffic by risk and criticality. Give developers a "second rocket" in mesh and critical systems powerful hubs. Tie everything into observability and clear processes. You’ll be surprised how much easier life becomes.
FAQ
Can mesh provide the same inspection as hub-and-spoke?
Yes, but selectively and architecturally: exit nodes, proxies, controlled egress points. It’s a hybrid approach. Full, blanket inspection is naturally easier on hub-and-spoke.
Which is faster: WireGuard in mesh or IPsec on a hub?
Depends on device and route. On a developer laptop, direct WireGuard peer links often win. On beefy hardware with encryption acceleration, IPsec can outperform, especially at gigabit speeds and above.
If NAT traversal fails, is mesh useless?
No. Relay nodes keep connections alive at the cost of added latency. Planning relay geography and monitoring relay traffic percentage is key.
Can DMVPN offer "almost mesh"?
Yes. Spoke-to-spoke tunnels via NHRP approach mesh experience, but control and policy remain at hubs. A solid compromise for traditional networks.
How to combine Zero Trust and hub-and-spoke?
Through proxy access, identity, NAC, segmentation, and app-level policies. Hub-and-spoke is transport and control; Zero Trust is access philosophy. They complement each other well.
What about long-term costs?
Mesh often cheaper initially and suited for knowledge work teams. Hub-and-spoke costs more in hardware and licenses but is predictable at scale and in regulated sectors. Consider total cost of ownership, not just monthly price.
What’s the safest migration strategy?
Hybrid. Start non-critical teams on mesh; keep hubs for the rest. Add observability, run incident drills, then expand. Don’t overhaul everything at once.
