VPN and Kubernetes Made Easy: Sidecar, Policy, Mesh, and Real-World Use Cases That Really Work
How to build a reliable VPN in containerized environments like Docker and Kubernetes: sidecar pattern, network policies, service mesh integration, eBPF tricks, secrets management, observability, and practical real-life examples. Up-to-date for 2026, no fluff — just proven solutions.
Content of the article
- Why we need vpns in containerized environments in 2026
- Docker and vpn: basic patterns and common pitfalls
- Sidecar pattern: vpn as a sidecar in the pod
- Kubernetes network policies: from basic isolation to fine-grained filtering
- Service mesh and vpn: who does what
- Vpn architectures for kubernetes: choose wisely
- Real-world cases: from sftp to multi-cloud and ci/cd
- Observability, performance, and debugging: can't skip these
- Security: secrets, keys, and access
- Implementation plan: step-by-step without chaos
- Performance optimization: simple steps, noticeable gains
- Incident debugging: a quick checklist
- Common mistakes and how to avoid them
- A mini-guide to choosing solutions
- Faq
Why We Need VPNs in Containerized Environments in 2026
Containers Speed Everything Up, but Networking Remains the Achilles' Heel
You’ve deployed microservices, everything’s flying — then suddenly your network to private resources drops. That stings. In 2026, we live in a multi-cloud world: Kubernetes clusters spread across regions, private APIs with partners, corporate databases behind firewalls, and regulatory demands. A secure and predictable communication channel is non-negotiable. VPNs aren't just tunnels; they're guaranteed corridors where no one interferes and we control the rules.
Containers change the VPN game: automation, isolation, clever routing, and policy integration are essential. Quick patches just don’t cut it anymore. We either do it systemically or make life harder for ourselves and support teams. The good news? There are proven patterns that scale effortlessly and keep DevOps smooth.
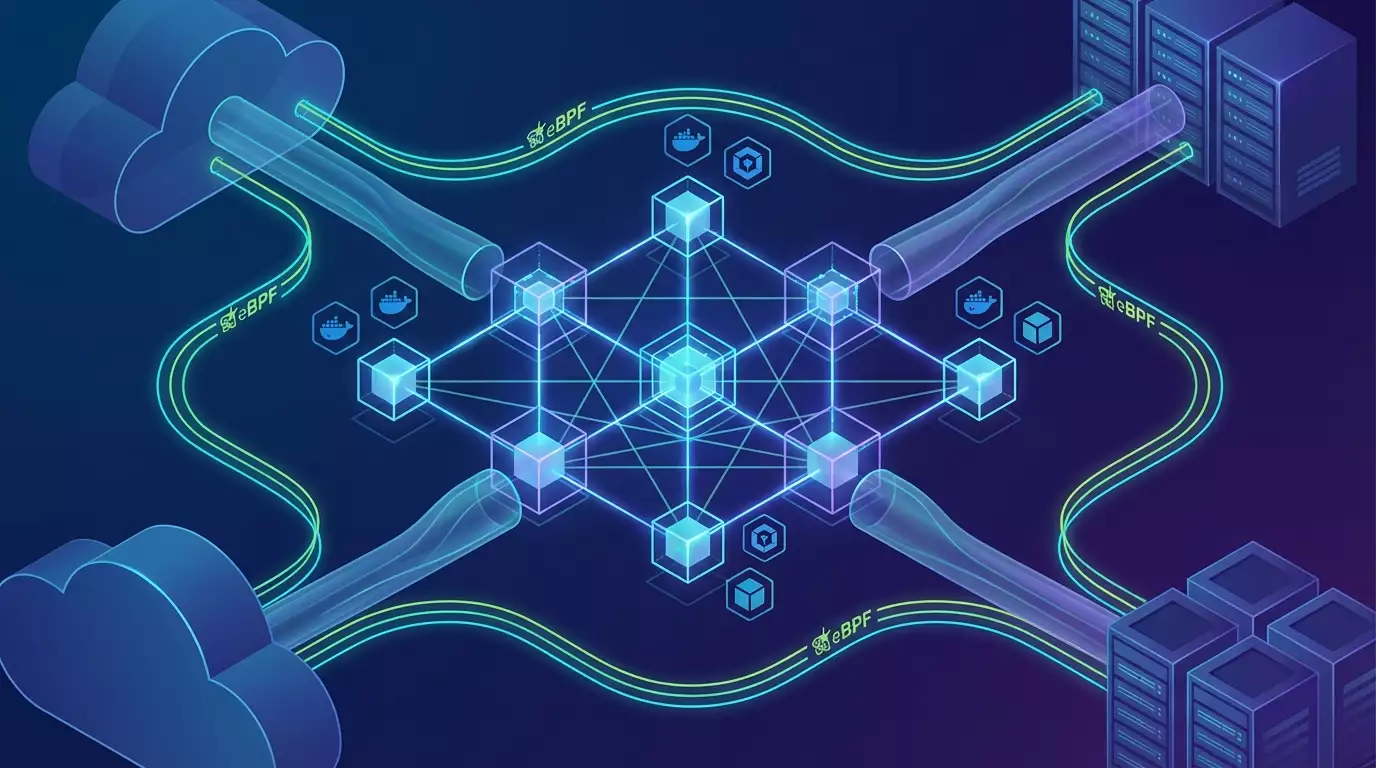
2026 Trends: eBPF, Sidecarless Data Planes, and Zero Trust
In 2026, eBPF has matured in production: network pools accelerate without iptables chaos, observability is deeper, and policies are more granular. There's a clear move toward sidecarless network planes for mesh, but traditional sidecars aren't going anywhere — they’re still handy when a local VPN and simple traffic isolation are needed. Zero Trust is no longer just a buzzword; it’s a set of practices: internal mTLS, external tunnels, and authenticating every hop.
One crucial detail: teams prefer managing networks through GitOps. Policies, tunnels, keys, routes — all in code with validation and audits. Not only neat, but also a solid way to minimize human errors.
Regulations and Cost Savings: Two Drivers Speeding Adoption
Regulators require data controls by region, connection logging, and routing justifications. VPNs with proper policies enable transparent reporting and smooth audits. Plus, cost savings: a well-planned tunnel and mesh replace expensive leased lines, while optimized routes cut latency without buying extra hardware. Simple and efficient.
Docker and VPN: Basic Patterns and Common Pitfalls
Containerized VPN Client: Fast and Isolated
The simplest approach is to run the VPN client (like WireGuard or OpenVPN) in its own container. You assign the needed capabilities (NET_ADMIN, SYS_MODULE if necessary, though it’s better without the latter) and bring up the interface in the container’s network namespace. Other app containers connect to it via a shared Docker network or through shared network namespace.
Pros: quick setup, predictable configuration, easy to scale. Cons: routing and DNS need careful tuning, or you risk all traffic going through the VPN—even when it shouldn’t. We usually go with split tunneling: only private subnets and hosts route through the tunnel; everything else goes direct.
Split-Tunneling and DNS Policy
Split-tunneling isn’t a luxury; it’s a must. If your CI downloads images from public registries, don’t funnel everything via VPN, or speed drops and traffic bills spike. The key is routing tables with priorities and correct domain rules. For DNS, use a local resolver in the VPN container or sidecar, so private zones go to the right upstream, and public domains resolve normally.
A common mistake: mixing resolver order. Result? Random timeouts and “sometimes it works” syndrome. We recommend explicit split-DNS lists and domain suffixes, plus health checks for critical domains.
Docker Compose: Minimal but Functional
In Compose, you can declare a vpn service with cap_add NET_ADMIN, mount configs, run WireGuard, and share network with the app via network_mode: service:vpn, or connect both services to the same bridge and set routing through the vpn. You don’t need fancy plugins; what matters most is careful default gateway and exception configuration. Again — split tunnels and DNS validation.
Experience shows that if you add a VPN health probe (like pinging a private host) and a graceful shutdown hook, you get predictable behavior during deploys and updates. Small details, big time-saver.
Sidecar Pattern: VPN as a Sidecar in the Pod
Why Sidecar at All When DaemonSet Exists?
Sidecar is your service's private bodyguard. It lives alongside in the same Pod, shares the network namespace (if configured), establishes the tunnel, and filters traffic locally. Maintenance is simple: isolate one service’s traffic from another’s, apply fine-grained policy, and leave the node host untouched. Sure, you can run a shared VPN via DaemonSet, but routing gets more complex and security slightly diluted.
Sidecar shines when a service depends heavily on private APIs or needs custom routes—like a payment microservice or partner SFTP integration. The sidecar runs the tunnel, serves only its neighbor, and doesn’t expose configs externally.
Routing and iptables Without Tricks
The concept is straightforward: the sidecar’s init container creates wg0 or tun0 interface, writes destination networks into routing tables, marks packets with iptables mangle rules to force selected CIDRs through the tunnel. The app works as usual, but its egress to private addresses goes via VPN. For ingress, you can similarly restrict sources, but usually VPNs focus on egress.
Tip: keep network lists in ConfigMap and version them via GitOps. Need to quickly expand the private list? Commit the change, ArgoCD or Flux picks it up, sidecar restarts — done. Smooth as butter.
InitContainers and Environment Setup
InitContainers are great for warming up routes, loading keys, and checking gateway availability. We often do this: init downloads and verifies keys from a secret store, validates configs, pings a control IP through the tunnel with a short timeout. If all good — start the main sidecar and app. Otherwise, crash fast so auto-healing restarts the Pod without holding a semi-zombie.
Kubernetes Network Policies: From Basic Isolation to Fine-Grained Filtering
Calico, Cilium, and eBPF Speed Up Policy Enforcement
Policies are your network’s seatbelt. Calico and Cilium have become standards. In 2026, eBPF is the preferred route for many because it’s faster and more flexible than iptables, plus offers rich telemetry without heavy overhead. But don’t chase trends blindly: if you have stable Calico with iptables and clear rules, no need to tear everything down just for a badge. Migrate on your schedule.
Bottom line: NetworkPolicy controls who can talk to whom and where egress can go. We pair it with the VPN sidecar: default deny everywhere, then allow egress to private networks only through the sidecar. This combo drastically reduces attack surface.
Egress Policies and DNS
Remember, egress policies work by IP/subnets only — not by domain. For private domain zones, use split-DNS and fix resolution through a local pod resolver. Or attach an egress-gateway (mesh), where you can enforce L7 policies tied to SNI. If you handle many FQDNs, egress-gateway is often easier: fewer headaches with ever-changing IP lists.
Multi-Tenant Namespaces
In multi-tenant clusters, without strong NetworkPolicies, any curious student might ping their neighbor. We usually apply this template: default deny on ingress and egress per namespace, network profiles for service groups, and isolated egress through a VPN sidecar. Plus a separate namespace for shared gateways accessible only from defined namespaces. It may seem boring, but it works rock-solid.
Service Mesh and VPN: Who Does What
mTLS Inside, VPN Outside
Mesh handles inter-service encryption and observability inside the cluster: mTLS, retries, timeouts, metrics. VPN secures the external corridor — to partners, private regions, and data centers. Don’t confuse the tools. In 2026, many use Gateway API and egress-gateway for outgoing L7 traffic control. Convenient: domain and path policies, JWT auth, and built-in tracing.
The combo looks like this: mesh with mTLS inside, VPN tunnels to needed networks outside, followed by an egress-gateway applying L7 policy and routing. This way, you know exactly who talks where and can quickly cut access without touching the app.
Istio, Linkerd, and Sidecarless Trends
Yes, sidecarless deployments are gaining ground, reducing overhead and simplifying troubleshooting. But for VPN, they’re not always ideal since a local tunnel and routing next to the app are often required. We often see hybrid setups: mesh manages policies and telemetry, VPN lives either in the sidecar or node agent for shared tunnels. Don’t get stuck in dogma — choose what’s easier for your team to maintain.
Egress-Gateway and L7 Policies
When private resources are accessible via HTTPS with SNI, the benefits really stand out. An egress-gateway lets you tie permissions to domain names and paths. Even if the IP floats, the policy remains valid. Beyond that is the network-level tunnel. This approach covers two risk layers: IP through VPN and L7 via mesh. Expensive? Not at all. Just grown-up networking.
VPN Architectures for Kubernetes: Choose Wisely
Hub-and-Spoke: Easier Than It Seems
The classic model: central hub (in a data center or cloud) with spokes to regions and clusters. Benefits include predictable management and simple key handling. Downsides: possible bottlenecks and added latency. In production, we often add a second hub, implement health-based failover, and route based on geography or ASN to the nearest hub.
Full Mesh VPN: When Direct Routes Matter
If you have many regions and latency is critical, direct tunnels between clusters solve it. Yes, keys are more complex, naming harder, and overlaps increase. But if your SLA demands tens of milliseconds, there’s no other way. In 2026, key orchestration and automatic config generation via GitOps make this manageable. No magic, but the routine becomes bearable.
Zero Trust: Trust No One, Verify Everything
Zero Trust with VPN means not one big tunnel for everything, but verifying identity and permissions at every step: device posture, short-lived keys, explicit policy authorization, and logging every request. VPN is just the transport; auth decisions live in mesh and access brokers. Concise and practical.
Real-World Cases: From SFTP to Multi-Cloud and CI/CD
Stable Access to a Partner’s Private API
Challenge: securely connect to a partner's API that uses IP whitelisting and strict rate limits. Solution: a sidecar with WireGuard, split tunneling only for the partner's CIDR, egress policy on the namespace, and a mesh egress-gateway with rate limiting and retries. Result: consistent 150-200 ms latency, zero timeouts, flexible limit tuning. Support is happy.
Multi-Cloud Replication
Two clouds, two clusters, one database replicated over private networks. We set a hub in the central region and build spoke tunnels to clusters. Inside: default deny NetworkPolicy, allow replication ports, traffic routed through VPN. Mesh applies mTLS and retry strategies to avoid stream breaks during hiccups. Peak latency rises 5-7 ms—tolerable and predictable.
CI/CD and Private Artifacts
The Kubernetes runner often struggles accessing private Nexus or Git servers. We add a sidecar with tunnel, warm up DNS and routes in init, block all unnecessary traffic with egress policy. Builds consistently fetch dependencies, no leaks outside. And yes, explicitly list hosts — saves your weekends.
Observability, Performance, and Debugging: Can't Skip These
Metrics That Actually Help
We track RTT to gateways, packet loss on tunnels, VPN vs direct traffic ratio, handshake errors, DNS resolve times for private zones. Plus basics: sidecar CPU/memory, descriptors, queues. Sounds dry, but when things break, these metrics tell you exactly where to dig.
Logs and Traces
VPN client logs flow into the centralized logging stack with key masking. App-level traces in mesh show stuck requests, which hop returned 429, and where things run smoothly. Matching latency spikes with packet loss graphs on tunnels makes troubleshooting crystal clear.
eBPF and Traffic Profiling
eBPF agents reveal actual VPN traffic flows versus bypasses. Invaluable for policy review: find your “gray cardinals”—services that unexpectedly send traffic outside. Fix policies, apply, check metrics, and sleep peacefully.
Security: Secrets, Keys, and Access
Stress-Free Secrets Management
VPN keys and configs belong only in secret stores: Kubernetes Secrets with KMS encryption, Vault, or cloud secret managers. No keys baked into images. No keys in Git. Sounds obvious, but trust us—we’ve seen it all.
Key Rotation and Short-Lived Tokens
Keys should have short lifetimes: automate rotation, get alerts days before expiry, failover through a secondary tunnel so updates don’t take down prod. Use blue-green deployment for VPN configs: new key, verify, switch, delete old. Split permissions: some can read, not write. Simple and secure.
Pod Security and Rootless Containers
Run VPN clients rootless when possible, minimizing capabilities. If NET_ADMIN is needed, grant only during init and revoke after. Use Pod Security Standards to lock down everything. Less trust in the container equals better sleep at night.
Implementation Plan: Step-by-Step Without Chaos
Audit Target Traffic and Map Flows
Start by taking inventory: which services talk where, domains, subnets, ports, and SLOs. Draw a flow map. Surprising insights often emerge here. Don’t scold your team — just document honestly.
Choose a Pattern and Run a Pilot
If you have few services and simple needs — sidecar. Need a shared perimeter — DaemonSet or node agent. Many domain policies? Egress-gateway plus mesh. Pilot in one namespace, enable metrics, monitor for a week. Then scale up incrementally.
GitOps and Change Control
All policies, routes, and configs go into a repo. Every change happens via PR and review. Artifacts are verified manifests deployed by CD systems. This avoids random tweaks and creates an audit trail—who changed what and why. Auditors and your own team will thank you months later.
Performance Optimization: Simple Steps, Noticeable Gains
MTU, MSS, and Packet Magic
MTU issues are common. Check path MTU discovery, set MSS clamping on tunnels to prevent fragmentation. Simple test: iperf through tunnel with varying packet sizes watching for losses. Nine times out of ten, a fine MSS tweak fixes “everything slows down in the evening.”
CPU and Cryptography
WireGuard is fast but encryption is CPU-heavy. Give the sidecar more vCPUs, enable hardware crypto instructions, avoid running it alongside heavy Java processes. Balance the load. Also, keep a couple of backup tunnels with lower route priority to avoid choke points.
DNS Caching and Warm-up
Local DNS cache in pods plus pre-warming critical domains reduce latency spikes. Cheap and effective. And remember to set reasonable TTLs, or you’ll fight cache invalidation with every record change.
Incident Debugging: A Quick Checklist
Start Simple
Ping the gateway, check reachability. Confirm private network routes point to tunnel interfaces. Test DNS: domain resolution targets, responders, and timeouts.
Dive Deeper
Review VPN logs, handshake statuses, key lifetimes. Check eBPF telemetry to see where packets really flow. Inspect mesh traces to identify break points in the chain.
Rollback If Needed
GitOps saves the day: revert to the last working set of policies and configs in minutes. No “what was changed?” drama. No panic. Everyone breathes easy. Then calmly analyze root cause.
Common Mistakes and How to Avoid Them
“One Tunnel for Everything”
Trying to push all traffic through one big VPN tunnel is admirable but inefficient. Split tunnels, domain-based egress rules, and tailored profiles per service are our way forward. More convenient, faster, and safer.
Ignoring DNS
DNS is a quiet saboteur. Check resolver order, use local caching, segment private zones. If DNS misbehaves, no policy will save you — “sometimes it works” persists.
No Metrics, No Control
Flying blind without metrics. Include must-have dashboards: tunnel health, low packet loss, acceptable latency, and adequate CPU. You’ll thank yourself later.
A Mini-Guide to Choosing Solutions
If You Have One Sensitive Service
Go with sidecar, split tunnels, strict egress policy. Plus foundational metrics and alerts. Simple and reliable.
If You Have Dozens of Services with Domain Rules
Add a service mesh with egress-gateway, L7 policies based on SNI, and use VPN as transport to private networks. Manage with GitOps, keep secrets in external stores.
If You Have Many Regions and Need Low Latency
Full mesh between clusters with automated key management, local hubs, and routing based on proximity. Watch MTU and CPU profiles carefully.
FAQ
Can I Avoid Sidecars and Use a Single Shared Node VPN?
Yes, it simplifies operations, but you lose pod-level isolation and routing flexibility. Fine for simple cases; sidecar is better for sensitive workloads.
Should I Switch to eBPF Immediately?
If your current policies work well and performance is good, migrate gradually. eBPF delivers benefits but don’t break what’s already working. Run pilots and transition slowly.
WireGuard or OpenVPN: Which to Choose?
WireGuard is faster and simpler, with excellent performance. OpenVPN offers more flexibility in some enterprise scenarios. We pick WireGuard 80% of the time, but evaluate based on your needs and compatibility.
How to Control Domain-Based Access if NetworkPolicy Works on IP?
Use an egress-gateway in your service mesh. It operates at L7, understands SNI, and enforces domain and path policies. This works well alongside VPN transport.
Where Should I Store VPN Keys?
In secret stores: Kubernetes Secrets with KMS, Vault, cloud Secret Manager. No keys in images or repos. Set up rotation and access audit.
How to Secure DNS?
Local cache in pods, explicit private zones, separate resolvers for internal and external domains. Add resolve metrics and timeout alerts to avoid mysterious failures.
Is Zero Trust Needed if We Have VPN?
Yes, because VPN is just transport. Zero Trust focuses on identity, authorization at every step, and least privilege. Together they provide real resilience and transparency.
