Network Segmentation via VPN in 2026: Microsegmentation, VLAN vs VPN, and Strict Isolation of Critical Infrastructure
Content of the article
- Why we need vpn-based segmentation in 2026
- Vlan vs vpn: what works when
- Microsegmentation and zero trust: the new security fabric
- Designing vpn-based segmentation: proven patterns
- Critical infrastructure and ot isolation: mistakes are fatal
- Tools and technologies 2026: what to choose
- Architectures and cases: from office to clouds and contractors
- Operation: visibility, testing, and policy as code
- Performance and user experience: no compromises
- Application-level security: network isn’t everything
- Implementation plan: where to start and how to avoid pitfalls
- Faq: brief and to the point
Why We Need VPN-Based Segmentation in 2026
Why Traditional Boundaries No Longer Hold
We used to think of the perimeter like a fortress wall. But look around: clouds, remote work, IoT, OT, and SaaS have blended into one living ecosystem. Traffic flows in hundreds of directions, users work from coffee shops, and critical data hops across regions and providers. In this fast-paced environment, the classic model of “one big network behind one big firewall” just doesn’t cut it anymore. We see this every day. Once an account is compromised, attackers start creeping inside. The perimeter is leakier than Swiss cheese. No exaggeration — that’s the reality.
So what really works? Segmentation. It doesn’t just slice the network into logical domains; it stops lateral movement and turns every network segment into a “bad apartment” for intruders. Add VPN as an encrypted, managed “corridor” between segments, and you get a flexible and secure topology. By 2026, this combo became the de facto standard: microsegments, Zero Trust, ZTNA, SDP, and finely tuned VPN tunnels that exist exactly where needed. Flexible, transparent, and predictable.
VPN as the Glue for Segments: Managed Connectivity Instead of Free Roaming
Instead of a flat network, we build a set of targeted paths. Want to access the staging database from the dev segment? Fine, but only through an authenticated tunnel, with the right port, verified identity, and only for the task’s duration. VPN stops being just an “all-purpose road” and becomes the fabric of policy: encrypting, tagging, limiting, logging. In this sense, “segmentation via VPN” sounds tautological, but that’s exactly how we trim spontaneous connections. There are no extra routes. And if tomorrow you migrate part of your infrastructure to another cloud, the VPN tunnels and segments move seamlessly with your policies.
The real win here is visibility and control. We don’t trap all traffic in one black box; instead, it flows over predictable routes. Logs become clearer, alerts more precise. If something drops, we instantly see the exact tunnel, policy, and segment. Response times shrink, and the risk of cascading failures goes down too. Plus, a nice bonus: security starts speaking the language of business. "This tunnel protects the payment gateway, SLA 99.95%." Sounds convincing, right?
Classic Fear: VPN Slows Things Down
A valid concern. Historically, IPsec and OpenVPN could cause noticeable performance hits. But today, we have WireGuard, kernel accelerations, hardware-accelerated ciphers, QUIC transport, and smart placement of points of presence. According to industry reports from 2025–2026, companies that properly deployed modern VPNs with mesh topology and dynamic routing reduced overhead to 5–10%, sometimes less. If segmentation is thoughtfully designed—not thrown together—performance doesn’t degrade. On the contrary, explicit policies and reduced broadcast domains boost stability and latency predictability.
VLAN vs VPN: What Works When
The Strength of VLAN: Speed, Simplicity, and Layer 2 Transparency
VLAN is the trusty hammer. It’s fast, usually hardware-accelerated, and manageable on switches. If you have a single campus, good fiber optics, and just want to separate departments or toolchains, VLAN fits perfectly. Apply policies, configure ACLs, enable DHCP snooping, Dynamic ARP Inspection, and many risks get trimmed. Routing between VLANs can be tightly controlled at Layer 3, minimizing attack surface. Need a quick “sandbox”? VLAN can spin up in minutes.
But VLAN has limits. It’s tied to Layer 2/3 domains; stretching it over WANs brings pain and complexity (VxLAN, EVPN, overhead). In multi-cloud and distributed branches, VLAN turns into a management headache, especially when teams are scattered and there’s no central network authority. We’ve seen organizations spend weeks just to extend a new segment through three providers. It costs time and nerves.
Where VPN Shines: Flexibility and Secure Connectivity Across Boundaries
VPN operates above IP and doesn't worry about Layer 2. Want to connect a cloud and a factory floor segment? No problem. Need temporary contractor access to a specific subnet? Easy. Modern protocols (WireGuard, IKEv2/IPsec, TLS/QUIC) don’t just encrypt traffic—they also tie to device and user identity. This lets you build thin, targeted communication paths without propagating broadcast domains or hauling along unwanted Layer 2 baggage. For distributed companies, it’s a revelation: one policy template, multiple presence points, and the tunnel lives exactly where business needs it.
Another plus—visibility. A tunnel is an entity you can measure, alert on, scale, and if needed, shut down within 10–15 seconds. We package risks into manageable containers. Matching flexibility with VLAN is tough. The resulting approach of “VLAN in the campus, VPN on the borders and between domains” has become the near “gold standard” in 2026. It combines the best of both worlds.
Transitional Model: Hybrid VLAN and VPN with Microsegmentation
Most real companies don’t do “either/or.” We see hybrids—VLAN for local cleanliness and throughput, VPN for intersegment and site connectivity, topped with microsegmentation where policy ties to identity. This scales well: add a new plant, it gets its VLAN, L3 ACLs, and a set of managed VPN tunnels to key services. Add a new cloud region, and you roll out the same policies living at the SD-WAN/SASE or ZTNA provider layer.
This isn’t theory. In one case, a manufacturing firm with 40+ branches cut new site onboarding from six weeks to five days thanks to VPN policy templates, preconfigured VLAN profiles, and automated PKI. Sure, there were bumps, but time to market won. That’s the real deal in 2026: business won’t wait.
Microsegmentation and Zero Trust: The New Security Fabric
Identity Beats IP: From Networks to Entities
Microsegmentation rethinks the very idea of a segment. Instead of “this subnet,” we say “this service,” “this process,” “this user.” Identity trumps IP address. Access ties to context: who you are, where you came from, how trusted your device is, if MFA is enabled, and posture status. Then a razor-thin access ribbon forms—no flashlight, but laser. VPN still acts as transport, but rules come from identity layers—ZTNA/SDP, sometimes eBPF agents on hosts, sometimes service meshes in Kubernetes.
The result? Lateral movement becomes very costly for attackers. Even if they capture credentials, without the right context and device validation, they get zero or minimal access. Plus, every access attempt is a visible event for SIEM and behavioral analytics. We effectively shine a spotlight in a dark room. It's uncomfortable for attackers and calming for us.
ZTNA and SDP vs Classic “All-Office” VPNs
Classic “fat” VPN grants users network access to large segments. In 2026, this looks like a gift set for lateral movement. ZTNA and SDP shift the paradigm: access is to the application, not the network. The client opens an encrypted channel to a broker, which checks context and passes traffic only to the target service. Want Jira? Get Jira. Need database? Only through a controlled proxy and on an approved client. No internal network scans—because the network simply “doesn’t exist” to the user.
This led to a practical compromise: ZTNA/SDP for users and external contractors, site-to-site VPN for services and integrations between segments, and microsegmentation on hosts (eBPF, host firewall, mTLS) for service-to-service communication. We layer control so attackers must break identity, broker, host policy, and network fabric sequentially. Expensive and noisy.
Microsegmentation Tech Stack
In 2026, the favored combo includes: eBPF agents filtering host traffic, mTLS for service-to-service encryption, service mesh (Istio/Consul) for Layer 7 policies, ZTNA/SDP for user-to-app, and WireGuard/IPsec for site-to-site. Policies are declared as code and tested before rollout. This isn’t an exaggeration: “policy as code” halves to triples incident counts by reducing human errors, based on large-scale transformation observations. We record intentions, run simulations, review diffs, and deploy without surprises.
The final touch—tying in IAM. Roles, attributes, groups, project membership fuel access policy. Change a role, change access. Contractor leaves? Their tunnel and tokens drop automatically. The beauty of simple things.
Designing VPN-Based Segmentation: Proven Patterns
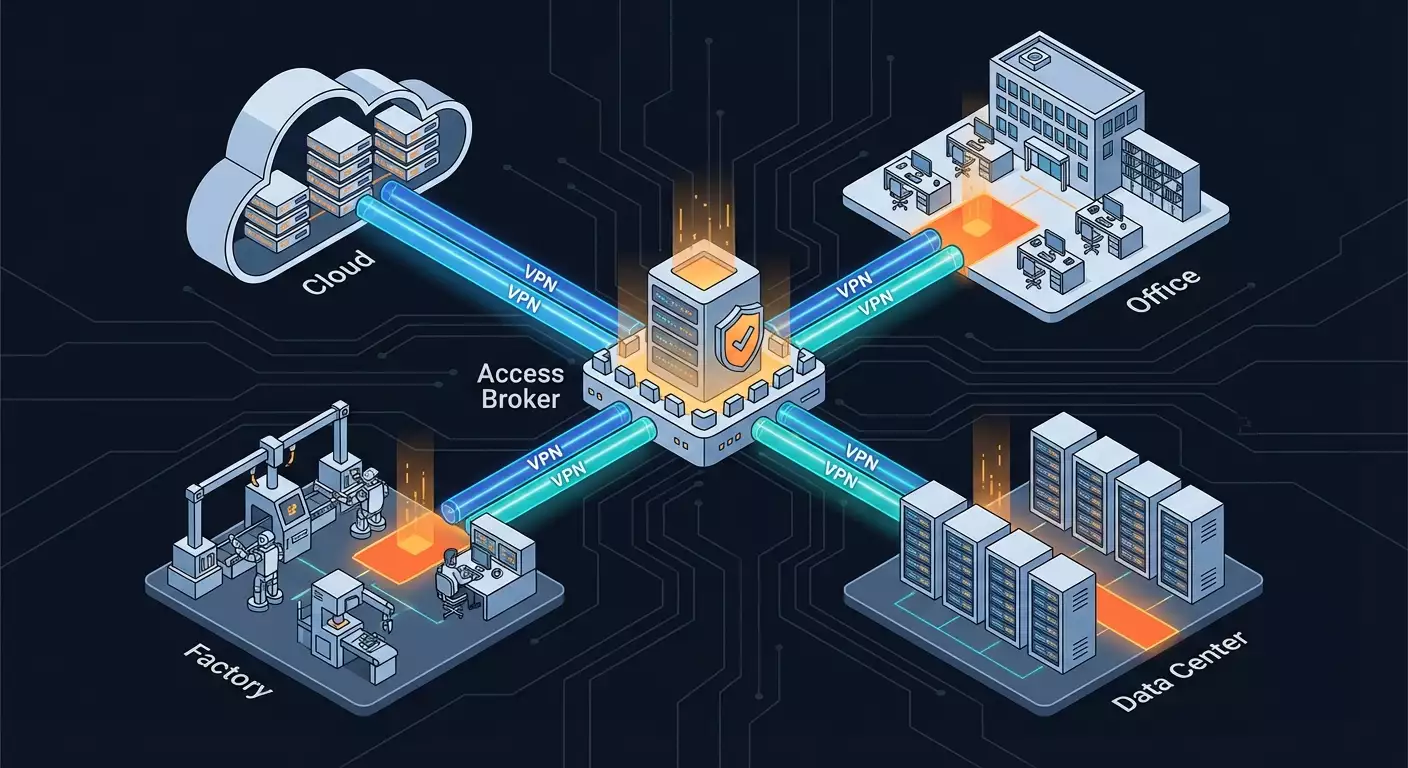
Pattern 1. Star with Access Broker and Narrow Tunnels
A central broker (one or more for redundancy) handles authentication, authorization, and telemetry. Edges are segments: offices, plants, clouds, DMZs. Between them, narrow VPN tunnels, each with a specific purpose: monitoring, replication, management, user app access. All tunnels tagged with metadata, policies declaratively applied. Critical segments get dual control: tunnels up only on request and approval, TTL 2–8 hours, packet-level and request logging.
Benefits: manageability. You see the map, you know each tunnel’s purpose. Growth means simply adding segments as new “leaves” of the star; the broker auto-distributes ACLs, policies, and certificates. Downside: requires solid SRE discipline and observability. Without them, the star becomes a “tape web.” But with automation—fantastic.
Pattern 2. Mesh Between Sites and Clouds
When traffic is multipoint and sensitive to latency, mesh solves it: each segment has a limited set of tunnels to neighbors by traffic nature, with dynamic routing. Important: don’t create a full mesh. Limit each node to 2–3 neighbors and keep transit tightly controlled. For example, a dev VPC in eu-central connects to staging VPC and CI/CD segment but not directly to prod. Prod tunnels only to essential shared services and disaster recovery sites. This keeps flexibility without chaos.
In 2026, mesh is conveniently built on WireGuard with dynamic control planes, layered over SD-WAN orchestration that accounts for channel metrics. QUIC transport offers good resilience to packet loss. You can add BGP over VPN with announcement restrictions. The key: policy comes first, routing second. Otherwise, you get route sprawl and hidden backdoor branches.
Pattern 3. Just-in-Time Tunnels with Strong Identity
For highly sensitive operations—admin tasks, registry access, controller updates—use JIT. Users request access, get a temporary role, and the broker spins up tunnels to specific IPs and ports with TTL. After expiration, tunnels collapse. Logs feed SIEM; on anomalies, SOAR shuts sessions early. This reduces constant segment exposure to near zero and, strangely, speeds up work: admins don’t hunt for “who left port 22 open on that server.” Everything is clear, by request, no surprises.
From experience: a mid-size bank’s JIT admin access to payment systems cut phishing-driven lateral movement success to zero over nine months. It’s not magic. The attacker has no persistent “door” or valid time window. Low chance, lots of noise.
Critical Infrastructure and OT Isolation: Mistakes are Fatal
Zones, Channels, Determinism
In OT environments, there’s no room for risk-taking. Value isn’t just data, but lives. Factory flows must be precisely scheduled. We divide infrastructure into zones by criticality and function, applying the “zone/channel” model from IEC 62443 practices. Transitions between zones pass through strictly controlled channels—usually VPN with DPI, proxies, and whitelist inspection. No “universal” tunnels to PLCs, no “convenient” RDP into ICS. Only proven protocol-port routes for scheduled maintenance.
We add physical and logical segmentation: distinct VLANs (sometimes separate Layer 2s), dedicated Layer 3 firewalls, protocol-level network screens, and narrow VPN tunnels to specific monitoring and update services. No broad allowances. Yes, all admin paths must be JIT with MFA, responsible approval, and packet-level monitoring. It’s not overkill; it’s essential.
Regulations and Compliance: NERC CIP, IEC 62443, Federal Law 152-FZ, PCI DSS
By 2026, auditors scrutinize not just paperwork but actual routes—topologies, logs, alerts. VPN segmentation fits well: isolated zones, managed channels, provable policies. Risks of unauthorized reads/writes minimized. Properly documented segmentation simplifies PCI DSS compliance for card payment segments by clearly limiting the CDE zone and documenting/logging access.
Challenges? Key and certificate management plus log retention. You must guarantee crypto resilience and immutable forensic trails. Many adopt dedicated WORM-storage and hardware root CA PKI. A must: periodic failover testing. Losing one access node shouldn’t crash the service. Surprisingly, many organizations in 2026 still don’t test access broker failures—and then say “oops.”
Case Study: Factory and Cloud MES
A manufacturing holding linked cloud MES to plants via VPN with strict Layer 7 validation. Each site got a dedicated VLAN for OT, a protocol translation gateway, and only two tunnels: monitoring and updates. Engineer access through ZTNA with JIT and job logging. Implementation took 12 weeks, zero downtime. A vital lesson: test your “rejects.” On pilot day one, the broker correctly blocked access to an unsigned firmware image. That saved dozens of investigation hours and possibly a production line break. Simple rule, real salvation.
Tools and Technologies 2026: What to Choose
VPN Protocols: WireGuard, IPsec, TLS/QUIC, and Post-Quantum
WireGuard became the de facto standard for site-to-site and host-to-host due to simplicity and speed. IPsec remains where network device compatibility and mature implementations matter. TLS/QUIC powers ZTNA/SDP products, ensuring stability over “tricky” networks. Cryptographically, validated post-quantum hybrid transitions are underway: classical ECDH combined with Kyber key exchange. Not fantasy—many vendors enabled hybrid profiles by 2025, and enterprises begin adoption on critical perimeters in 2026.
Performance matters. Our measurements show WireGuard on modern kernels with offload delivers high throughput with 3–8% CPU overhead under stress. QUIC excels in lossy, variable latency environments. IPsec is solid with hardware acceleration on routers. Key: don’t marry one protocol for all tasks. Use the right tool for the job to balance speed and functionality.
ZTNA, SDP, SASE, and SD-WAN: Building a Modular System
ZTNA grants app access based on context. SDP hides infrastructure, raising tunnels only for verified sessions. SASE merges networking and security services in the cloud, simplifying global policy delivery. SD-WAN manages traffic and optimizes channels. In 2026, top deployments are not “one or the other,” but smart combos. For example, users authenticate through ZTNA, services interconnect over WireGuard mesh, branches connect via SD-WAN with hybrid channels, and internet-bound traffic routes through SASE gateways with CASB and DLP.
Sound complex? Yes. Hence automation and policy unification are crucial. Define rules once, and the system propagates them across network, transport, and application layers. Integrate scenarios into CI/CD pipelines: before releasing a service, run policy simulators, see segmentation impact, tunnel needs, introduced risks. Discipline pays off hands down.
NAC, IAM, MFA, EDR, SIEM, and SOAR: The Connected Orchestra
Without strong IAM, segmentation becomes messy. Roles, attributes, groups, automatic deactivations—it’s foundational. NAC controls who enters local VLANs and under what conditions. EDR monitors host health to validate “trusted device” status isn’t just talk. SIEM collects events; SOAR responds—cutting tunnels, rerouting, terminating sessions based on indicators. One source of truth needed—a single object and role dictionary. When IAM declares “this is shift engineer in zone A,” all systems know the exact access and tunnel setup.
Time is critical. We measure success by automated responses without manual intervention and MTTR. A good 2026 goal is terminating suspicious sessions within 60–120 seconds after multiple triggers fire. Hard, but achievable if segmentation and VPN are managed alongside SOAR—otherwise, you’ll be “sending emails to network ops” and losing precious minutes or hours.
Architectures and Cases: From Office to Clouds and Contractors
Corporate Network with Branches and Remote Work
Start simple: headquarters, three branches, hundreds of remote workers. Locally—VLANs by function, intersegment ACLs. Between offices—SD-WAN with two providers. Users connect via ZTNA, each application granted on a least-privilege basis. Branches and data center linked by site-to-site VPN profiles. Contractor access is JIT and limited to necessary services with mandatory device validation. This keeps the framework simple and manageable.
Results? 40% drop in incidents over six months compared to legacy VPNs, per internal security stats. Branch onboarding time shrank to 4–7 days from 3–4 weeks. Users stopped seeing the “whole network,” only their apps, simplifying support. Fewer “why can’t I ping 10.0.0.14?” questions. Thank goodness.
Hybrid Cloud and Multi-region
The cloud side is a set of VPCs/VNETs with small blast radii. Prod isolated; staging and dev connect only to shared services—logging, billing, artifacts. All cloud-to-on-prem connections via VPN; cross-cloud regions linked with limited-degree mesh. Kubernetes runs service mesh with mTLS and Layer 7 policies; separate north-south gateways with WAF. Admin access through ZTNA, no direct cluster entry. Even SRE emergency tasks go through JIT.
Outcome—incident containment. Once a harmful dependency in dev was detected. Policies blocked it from prod metadata and internal APIs. Noise yes, but the system held because the network clicked together as controlled channels, not a “single sea.” That’s VPN segmentation and microsegmentation in action: a “fire” doesn’t become a “forest fire.”
Contractors, Temporary Teams, Auditors
Contractors can be tough. Their laptops, habits, sometimes risks. We restrict their access to the app layer: ZTNA grants exactly what’s needed, only from trusted environments (VDI or registered devices), fully audited. For audits, we open temporary tunnels with clear descriptions: “SOC2 audit, CDE zone, read-only, TTL 72 hours.” When over, everything collapses automatically. No need to remember who to cut off post-project—the system handles it.
In a large financial audit case, this approach saved 14 person-days of manual access handling, relieved IT, and eliminated “forgotten accounts.” Auditors praised the transparency: all permissions visible, logs present, responses quick. In compliance world, that’s rare and earns goodwill points.
Operation: Visibility, Testing, and Policy as Code
Telemetry and Security SLOs
If you don’t measure, you guess. For VPN segmentation, define key SLOs: tunnel setup time, successful auth rates, latency on critical paths, cumulative broker and node uptime. These metrics aren’t just for security—they let business detect weak spots and guide investments. Best practice: publish monthly “security networking” reports with metrics, incidents, and enhancements. Over time, patterns emerge and bugs hidden for years get caught.
Tools? Export metrics from VPN control planes, ZTNA, SD-WAN, and service mesh into a unified TSDB, correlate in SIEM, alerts into SOAR. Don’t chase perfection; start with 5–7 clear metrics and aim for automatic responses. Example: payment tunnel degradation triggers a failover reservation, notifies SRE, restricts noncritical flows. Simple. Effective.
Policy as Code and Simulations
Policy as code is the best friend of network segmentation. Define desired connections declaratively, store in a repo, review, test, then deploy. Simulators reveal changes: which tunnels form, what ACLs narrow, what breaks. Errors caught pre-release save hours and nerves. Classic scenario: dev engineers mistakenly get staging access. Simulator flags risk; developers fix it. Five-minute chat beats overnight outage.
Many use a unified DSL for ZTNA, SD-WAN, service mesh, and NAC policies. Integration isn’t perfect, but the pipeline works. Linters and security policies run in CI. Initially tricky, then indispensable. Not empty words.
Failover Plans and Drills
Broker failure? VPN node down? PKI error? Drill them quarterly: “burn” primary broker, spin up backup, switch channels to fallback providers, manually test JIT processes. Docs help, but muscle memory helps more. Teams that train restore access in 5–15 minutes; those relying on docs take hours. Huge cost and stress differences.
The secret: make drills engaging and realistic. Add partial failures, “human” errors, simulate policy rollbacks. The team learns to value automation and spots “weak seams.” This is the only way to prove your segmentation won’t crumble when the world gets noisy.
Performance and User Experience: No Compromises
Route and Presence Point Optimization
To avoid VPN bottlenecks, locate presence points close to users and services. Equip SD-WAN with latency and loss-based path policies. Use split tunneling wisely: don’t route all internet via corporate center if cloud SASE gateways already inspect traffic. Microsegmentation helps—fewer all-encompassing flows, more targeted paths. Result: lower latency, higher stability.
Try QUIC in high-loss scenarios. It performs well in mixed networks. Also cache policies on ZTNA clients—when internet fluctuates, users don’t feel “everything’s down.” Small wins add up to great business ratings, which help when asking for next quarter’s budget.
Access UX: Clear Errors and Self-Service
Users shouldn’t guess why they’re locked out. Give clear messages: “Insufficient rights. Request Role X,” or “Device doesn’t meet requirements: enable disk encryption.” Add a self-service portal for JIT requests with approval SLAs. Simplify the path: the easier to get proper access, the fewer workarounds and shadow IT. Good UX cuts helpdesk tickets by 20–35% in practice.
Don’t forget mobility. ZTNA clients and light VPNs must work equally well on laptops and phones. Phones today serve as a backup channel for critical ops. Funny but true: one incident was resolved from a taxi via phone because JIT and MFA were just two taps away. Installing heavy clients would have meant a sad ending.
Reliability: N+1, Caching, Graceful Degradation
Design for resilience everywhere. Access brokers must have hot standby, policy caches on clients survive brief control plane losses, PKI pipelines hold offline keys and rotation plans. Graceful degradation means the service wheezes a bit but doesn’t crash. You can’t guarantee 100% uptime, but you can make failures short and understandable with clear workarounds. Business appreciates that.
Example: policy cache lives 15 minutes without broker; after that sessions require refresh. It’s a balance between security and availability. You can be stricter or looser. This is a classic case where “perfect” is the enemy of “good.”
Application-Level Security: Network Isn’t Everything
mTLS, Service Mesh, and Explicit Layer 7 Boundaries
No matter how segmented the network, if services trust anyone, trouble’s inevitable. By 2026, mTLS between services with certificate rotation via mesh is standard. Layer 7 policies define who talks to whom and what methods, paths, headers are allowed. We minimize unknowns. Even if the network slips and passes an errant packet, Layer 7 blocks the action. This second security layer makes microsegmentation much stronger.
Of course, it requires app teams to discipline themselves. They resist, debate, but after a quarter admit: resilience improved, incidents localize, debugging speeds up. When applications also take responsibility, the network becomes simpler and more predictable. Honestly, it just breathes easier for all of us.
Data: Classification, DLP, Tokenization
You can’t protect everything equally. Conduct honest data classification and align access policies with data classes. Personal data gets one set of segments and channels, payments another, R&D yet another. DLP on SASE gateways and email, tokenization for external integrations, end-to-end encryption for highly sensitive data sets. Remember: network isn’t a magic box. If an app leaks data outward, no VPN will save you. Work together with data owners, not instead of them.
Interesting 2026 trend: “privacy by design” in network policies. Traffic is private by default, logs anonymized, disclosures only by request with proper role and audit. Secrecy stops being a “mode” and becomes a system state. We like that.
Supply Chain Attacks: Least Trust by Default
Supply chain is the top headache of recent years. We integrate external APIs, deploy images, run agents—but what guarantees? VPN segmentation helps, but the last barriers are whitelists for outbound directions, artifact validation, SBOMs, and sandboxes for new components. External providers get exactly one tunnel to a defined service. Any bypass triggers SIEM events. Some partners struggle, but let that be your maturity filter. Security isn’t a place for luck-based compromises.
Good practice: monthly “friendship checks” reviewing all external tunnels. What’s active, who owns it, why needed. Remove trash mercilessly. The truth is simple: a closed tunnel can’t be hacked.
Implementation Plan: Where to Start and How to Avoid Pitfalls
Inventory and Dependency Mapping
Start with inventory. Services, users, data, dependent systems, external links. Draw flow maps: who talks to whom and why. Without this, segmentation is guesswork. Always highlight critical paths separately: payments, management, logs, emergency comms. We often find “hidden” dependencies used once a month by some person. Then those routes break and everyone’s surprised. Maps remove surprises.
Tools are simple: network analysis, log collection, team surveys, agent monitoring. Boring, yes. But skipping this step costs more later. The devil’s in the details, and segmentation is all about details.
Pilot, Scaling, and Standards
Run a pilot in a limited domain: one branch, one cloud segment, one critical service. Test access, JIT, user ZTNA, service mesh. Measure before-and-after metrics: latency, incidents, MTTR. Base templates on facts: tunnel profiles, IAM roles, eBPF policies, Layer 7 rules. Package recurring elements into standards. After that, scaling is a process, not a project.
Don’t forget the “junk” stuff. You’ll find legacy rules, opaque ACLs, orphaned services. Clean them up. Ghost cemeteries cause leaks and failures. Review policies monthly. It’s network relaxation.
Training and Culture
People matter more than boxes. Train engineers, product teams, support. Explain why “one big VPN” is gone. Show how JIT and requests work. Make a cheat sheet one-pager. Set security KPIs but don’t punish honest mistakes. The team must believe policy helps, not hinders. Then you’ll succeed even if it seems “hard and long” at first.
Culture shows in respect for process. If a boss asks “just give me everything, I’m the boss,” it’s a system test. Honestly: sometimes you explain three times. But when people see transparency and speed in correct access, resistance fades. That’s a no-return path.
FAQ: Brief and to the Point
What’s the difference between VLAN and VPN for segmentation, and can one suffice?
VLAN splits local network into Layer 2/3 domains, great for campuses and data centers needing fast traffic without WAN. VPN builds secure channels over IP, flexibly connecting remote segments, clouds, and branches. In 2026, the hybrid wins: VLAN for local clarity and performance, VPN for intersegment and inter-site links, with microsegmentation and Zero Trust on top. Using only one tool almost always brings compromises: scaling pain or isolation gaps.
Does microsegmentation require ZTNA and eBPF, or can you start simpler?
You can start simple: tighten Layer 3 ACLs, remove universal access, implement JIT for admin tasks. Then add ZTNA for users to grant app rather than network access. eBPF agents and service mesh give finer Layer 7 and host control but can roll out gradually. Layered strategy beats big bang. Key: tie access to identity and context, not IP address.
Will performance drop significantly moving to VPN mesh and ZTNA?
If designed right—not much. WireGuard and hardware-accelerated IPsec handle high speeds; QUIC withstands packet loss; SD-WAN and local presence points cut latency. Companies often see 5–10% overhead with correct setup and split tunneling. Segmentation can boost stability by shrinking broadcast domains and eliminating unnecessary paths. Test early and pick protocols per task.
How to isolate critical infrastructure when PLCs need periodic updates and telemetry?
Divide OT into IEC 62443 zones, ensure strictly controlled channels. Use narrow VPN tunnels only with whitelisted protocols and ports; enable JIT for admin ops with MFA and logging. Telemetry flows via dedicated monitoring segment; updates go through separate signed-payload channels. No universal tunnels. This minimizes exposure and maintains process determinism.
Should post-quantum cryptography already be included in VPN?
Yes, for external and long-lived channels, consider hybrid key exchanges (e.g., ECDH+Kyber). Vendors included hybrids by 2025, and rollout is ongoing in 2026. This reduces “collect now, decrypt later” risk. For internal short-lived tunnels, phase rollout plans. Pilot, check compatibility, measure overhead. No panic, but neglect isn’t wise.
How to prove segmentation via VPN pays off to the business?
Speak numbers. Show incident drop, MTTR reduction, faster branch onboarding, fewer manual access tasks. Tie tunnels to critical service SLAs: "this channel protects payments, 99.95% uptime." Share cases where microsegmentation stopped lateral movement or lowered support load. With metrics and real stories, budgeting become risk management, not abstract “security for security’s sake.”
